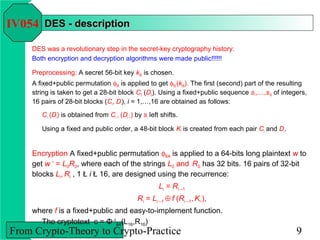
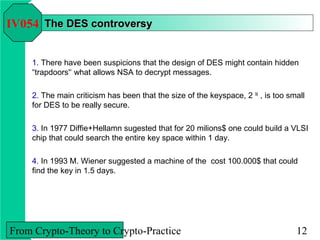
PPT – CHAPTER 12: From Crypto-Theory to Crypto-Practice I PowerPoint presentation | free to download - id: 75d5ce-YmIwN

Brain regional vulnerability to anaesthesia-induced neuroapoptosis shifts with age at exposure and extends into adulthood for some regions - British Journal of Anaesthesia